I found an interesting example today where the double quote is banned inside of the value parameter.
<input type="text" value="[input]">Typically there is no solution to this because attackers are not able to escape the double quotes, and therefore everything will be the value including brackets.
I.E. the following form is not working
<input type="text" value="<script>alert</script>">However, the situation gets dramatically change if there is a tag that has higher priority than input tag.
For example,
<textarea><input type="text" value="[input]">At this time, though we are still not able to use double quotes to escape, we can use </texarea> to escape
<textarea><input type="text" value="</textarea><script>alert(1)</script>">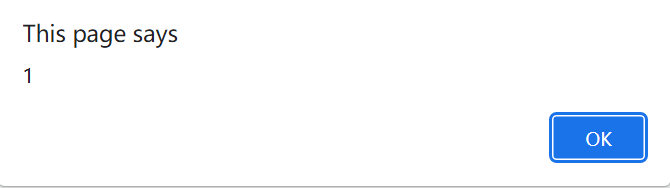
The similar “high priority” tags include
<!--,<iframe>,<noframes>,<noscript>,<script>,<style>,<textarea>,<title>,<xmp>TODO:
Read https://bishopfox.com/blog/lexss-bypassing-lexical-parsing-security-controls, which contains more scientific explanation towarding “priority”